GCVE BCP-07 – First Implementation in Vulnerability-Lookup
We are excited to announce the successful implementation of GCVE BCP-07 in Vulnerability-Lookup, marking the first production-grade adoption of this Best Current Practice within an operational vulnerability intelligence platform.
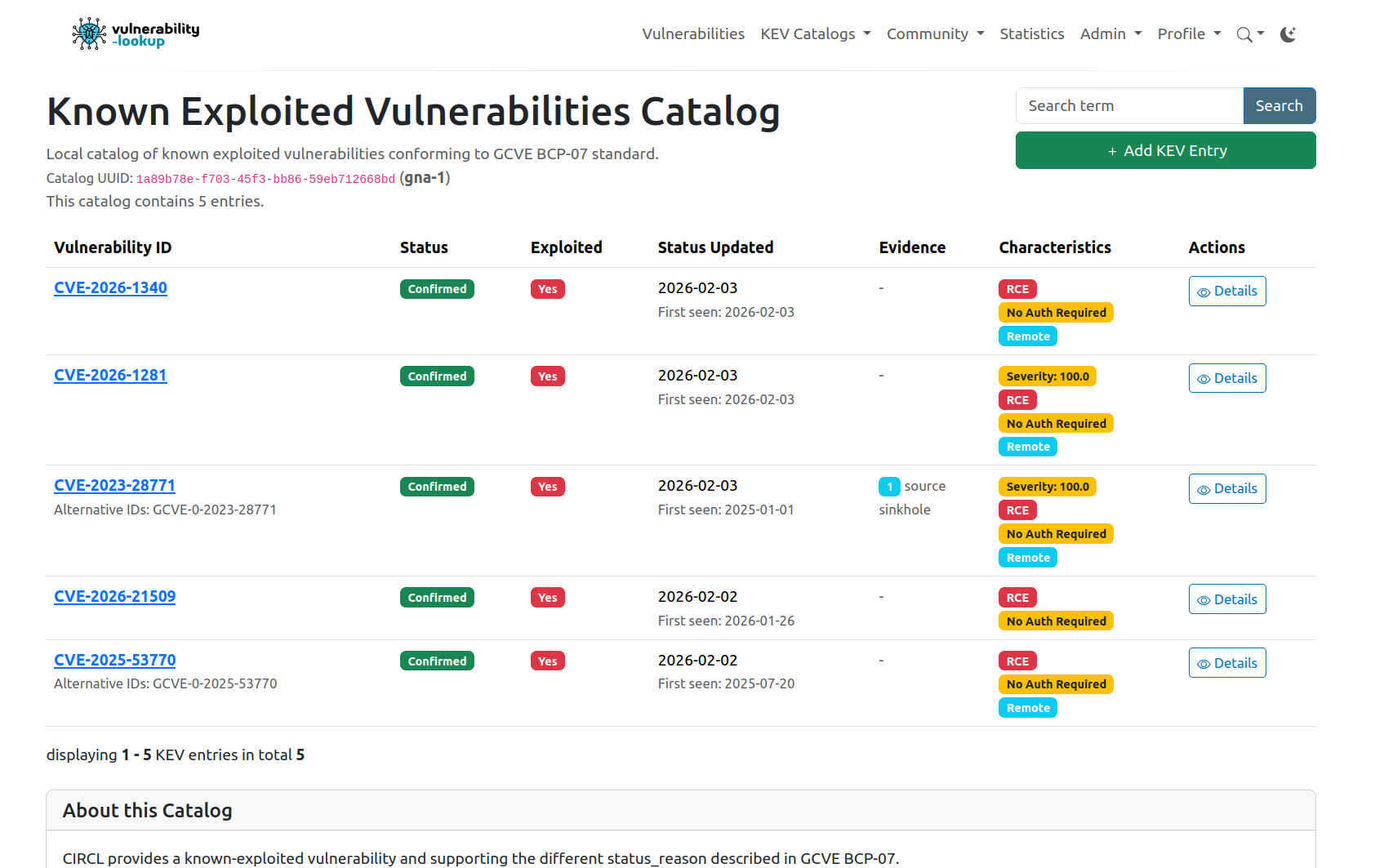
With the release of Vulnerability-Lookup 3.0.0, GCVE BCP-07 moves from specification to reality. This release introduces native support for federated Known Exploited Vulnerabilities (KEV) catalogs, fully aligned with the GCVE framework.
👉 Read the Vulnerability-Lookup 3.0.0 release announcement
From Centralized Lists to Federated KEV Intelligence
GCVE BCP-07 was designed to address a structural limitation of traditional KEV lists: their centralized nature and lack of contextual attribution. While such lists are invaluable, they often do not clearly express who observed exploitation, under which conditions, and with what level of confidence.
BCP-07 introduces a simple but powerful shift:
- KEV information is published by Global Numbering Authorities (GNAs)
- Each assertion is explicitly attributed
- Multiple perspectives can coexist without conflict
- Consumers decide which sources they trust
Vulnerability-Lookup 3.0.0 is the first platform to fully operationalize this model.
KEV Federation, Out of the Box
Any Vulnerability-Lookup instance can now:
- Publish its own GCVE-BCP-07–compliant KEV catalog
- Consume KEV catalogs from other GNAs
- Present multiple KEV perspectives side by side, transparently and consistently
This is not a theoretical capability. It is live and in production today.
KEV catalogs already available
-
CIRCL KEV
https://vulnerability.circl.lu/known-exploited-vulnerabilities-catalog/ -
ENISA KEV (EUVD / CSIRTs Network)
https://vulnerability.circl.lu/known-exploited-vulnerabilities-catalog/?catalog_uuid=cce329bf-df49-4c6e-a027-80be2e6483bd
The GCVE-operated instance, available at
👉 https://db.gcve.eu
is fully synchronised with these catalogs and demonstrates the federated model in action.
The reference file is available at:
https://gcve.eu/dist/references.json
And is localy cached in all Vulnerability-Lookup instances thanks to the GCVE Python client (included in Vulnerability-Lookup)
Why This Matters for the Cybersecurity Community
For organizations involved in vulnerability management, incident response, and risk prioritization, GCVE BCP-07 enables:
- Clear provenance of exploitation claims
- Parallel intelligence streams from multiple trusted authorities
- Reduced dependency on a single centralized source
- Greater resilience against outages, delays, or blind spots
Federation is not just an architectural choice — it is a strategic one. In a landscape where exploitation signals are often sparse, bursty, and context-dependent, robustness comes from diversity and transparency of sources.
GCVE BCP-07 enables exactly that.
A Collective Effort
This first implementation would not be possible without the continued commitment of organizations that openly publish KEV data.
A warm thank you to CISA and ENISA for their sustained efforts and for making their KEV information available to the global community. Their contributions are foundational building blocks for effective vulnerability prioritization and collective cyber defense.
The future
GCVE BCP-07 is now implemented, operational, and federated.
We look forward to seeing more GNAs, platforms, and organizations join this growing ecosystem.